12.3 Testing & Maintenance
AS Level · 26 questions found
What this topic covers
Section titled “What this topic covers”- Error types: syntax, logic, run-time — locate, identify and correct
- Testing methods: dry run, walkthrough, white-box, black-box, integration, alpha, beta, acceptance, stub
- Test strategy, test plan and their likely contents
- Test data types: normal, abnormal and extreme/boundary
- Maintenance types: perfective, adaptive, corrective
- Analyse and amend an existing program to enhance functionality
Past paper questions
Section titled “Past paper questions”A program monitors the speed of vehicles as they move around a large building site.
Each vehicle contains a sensor which reads an integer value that represents the speed of the vehicle. The value is expected to be in the range 0 to 60 inclusive.
The sensors cannot read values less than 0.
A program module has been written to validate the values read by the sensors.
(a) A test plan is needed to fully test the module. 4 marks
Complete the table. The first line has been completed for you.
Assume the sensors generate only integer values.
| Type of test data | Test data value | Expected outcome |
|---|---|---|
| normal | 36 | data item is accepted |
(b) Each sensor used in the system has a unique sensor ID number in the range 1 to 50. 8 marks
The program that is used to monitor the speed of each vehicle reads each sensor value every second and stores this value along with the sensor’s unique ID into a global 2D array Reading
The global array Reading has been declared as follows:
DECLARE Reading : ARRAY[1:2000, 1:2] OF INTEGER
The array contains 4000 elements organised as 2000 rows and 2 columns.
Column 1 contains the sensor value, and column 2 contains the sensor ID.
When 2000 sensor readings have been taken, the array is full and the system stops taking any more sensor readings until the array has been processed.
A procedure Sort() is needed to sort the array into ascending order of sensor value using an efficient bubble sort algorithm.
Write efficient pseudocode for the procedure Sort()
Show mark scheme
6(a) [4 marks]
Type of test data Test data value Expected outcome 36 data item is accepted 0 / 1 data item is accepted 59 / 60 data item is accepted
= 61 data item is rejected 15 data item is accepted and Value and Outcome)
6(b) [8 marks]
1999 TRUE 1 TO Boundary Reading[J, 1] Reading[J+1, 1] Temp Reading[J, 2] Reading[J+1, 2] Temp FALSE Boundary - 1 Procedure heading and ending Conditional loop correctly formed including Boolean flag declared and An inner loop Correct range 1 to 1999 for inner loop Comparison of element J with J+1 in a loop Declare variable and swap elements in a loop Temp Both SensorID and Speed values were swapped in a loop 'No-Swap' mechanism: • Conditional outer loop including flag reset • Flag set in inner loop to indicate swap Reducing in the outer loop Boundary
A program is being developed to control the production line in a factory.
(a) A number of different program life cycles are available for the development of a program.
(i) Explain the need for different program development life cycles. 1 mark
(ii) Coding is a stage in a program development life cycle. 1 mark
State one consideration that would influence the choice of programming language.
(b) The program has been in use for a number of months and adaptive maintenance is required.
(i) Give three reasons why adaptive maintenance may be required. 3 marks
1
2
3
(ii) As well as adaptive maintenance, other types of program maintenance may be needed. 1 mark
Identify one other type of program maintenance.
Show mark scheme
1(a)(i) [1 mark]
One mark for Choice of program development cycle depends on the approach/method required to produce the program Or One mark for a factor that would influence the choice of program development cycle, e.g. • Rapid development of program/prototypes required • Need for prototypes (at an early stage) • Complexity of problem • Skills / experience of development team / programmer(s) • Budget / Time / Resources available • Size of development team • Developer / programmer can return to earlier stages / any stage • Avoidance of repeating previous stages in development of program • How much involvement clients will have • Allows the (program) requirements to be changed during program development • (Program) requirements agreed at start of development of program Max 1
1(a)(ii) [1 mark]
Which programming language would best be suited to control the production line // Which programming language would best suit the problem being solved
1(b)(i) [3 marks]
Examples include: • Change to (production line) requirements • New technology / hardware available (to control production line) • Changes made to library modules used • Change in relevant legislation Max 3
1(b)(ii) [1 mark]
Perfective // Corrective
1(c) [4 marks]
1 mark for each correct row Expression Data type RIGHT(MachineCode, 4) STRING Speed * 2.5 REAL NOT Status BOOLEAN IS_NUM(Check) BOOLEAN
1(d)(i) [1 mark]
Two / 2
1(d)(ii) [1 mark]
1000 DECLARE Product : ARRAY [0:99, 0:9] OF INTEGER
1(d)(iii) [2 marks]
1 mark for correct upper and lower bound • [0:99, 0:9 1 mark for all other parts of declaration DECLARE Product : ARRAY [0:99, 0:9] OF INTEGER
A software developer follows a program development life cycle. The life cycle divides the development process into various stages.
(a) The following table lists some development activities. 5 marks
Complete the table by writing the name of the life cycle stage for each activity.
| Activity | Name of life cycle stage |
|---|---|
| The walkthrough method is used. | |
| An algorithm is implemented in a programming language. | |
| The client is interviewed about problems with the current system. | |
| The program is modified to run on new hardware. | |
| Records and file structures are defined. |
(b) The program contains a validation function.
(i) The function will: 4 marks
take an integer value as a parameter
return TRUE if the value is within the range 24 to 37, inclusive
otherwise return FALSE.
Complete the table to define a test plan to thoroughly test the operation of the function.
| Type of test data | Test data value | Expected result |
|---|---|---|
| Normal | 30 | TRUE |
(ii) The function is to be tested on its own. When it is shown to work correctly the function will be combined with other modules and testing will continue. 1 mark
Identify the type of testing that this represents.
Show mark scheme
5(a) [5 marks]
Name of life Activity cycle stage The walkthrough method is used. Testing An algorithm is implemented in a programming language. Coding The client is interviewed about problems with the current Analysis system. The program is modified to run on new hardware. Maintenance Records and file structures are defined. Design One mark per row
5(b)(i) [4 marks]
One mark per row Type of test data Test data value Expected result Abnormal 12 (< 23) FALSE Abnormal / Boundary / Extreme 23 FALSE Boundary / Extreme 24 TRUE Boundary 25 TRUE Boundary 36 TRUE Boundary /Extreme 37 TRUE Abnormal / Boundary / Extreme 38 FALSE Abnormal 99 (> 38) FALSE Max 4 marks
5(b)(ii) [1 mark]
Integration (testing)
A program has been developed and released for general use. After a few months of use an error is detected where under certain circumstances it outputs an unexpected value.
(a) The error in the program needs to be corrected. 1 mark
Identify the stage of the program development life cycle that this correction is made in.
(b) The program contains a function Lookup(). After investigation, it is found that this is the function that sometimes returns an incorrect value. 3 marks
An Integrated Development Environment (IDE) is used to help locate the error.
The IDE features of watch window, single stepping and breakpoint will be used.
Explain these features including the order that they will be used in to locate the error in Lookup().
(c) To solve the error a programmer decides to create a new module. 2 marks
The design of the new module has been completed and the module is being coded.
Identify two features of an IDE that will help during the coding of this new module.
1
2
(d) The new module referred to in part (c) introduces three new variables. 3 marks
Complete the following table by giving the appropriate data type for each.
| Variable name | Used to store | Data type |
|---|---|---|
| Name | A customer name. | |
| Index | An array index. | |
| Result | The result of the division of any two non-zero numbers. |
Show mark scheme
1(a) [1 mark]
(Corrective) Maintenance
1(b) [3 marks]
For example: • Set a breakpoint at the start of / within to stop execution at a Lookup, given statement • then use single stepping to execute one statement / instruction at a time • to display the value of variables using a watch window One mark for each: MP1 Order starting with a breakpoint and an explanation – ‘stop execution at this statement / line’ MP2 Explanation of single stepping – execute ‘line by line’ / statements MP3 Explanation of watch window – displaying the value of variable(s)
1(c) [2 marks]
Features include: MP1 Editor MP2 Auto
(syntax) complete / auto correction // identify undeclared variables(s) MP3 Prettyprint / auto-indentation / auto (structure) highlighter MP4 Dynamic syntax checking MP5 Expand / collapse code blocks MP6 Context sensitive prompts Max 2 marks
1(d) [3 marks]
One mark per row: Variable name Used to store Data type Name a customer name STRING Index an array index INTEGER the result of the division of any two non-zero Result REAL numbers
A program contains a global 1D array Data with 100 elements of type INTEGER.
The program contains a function Process() expressed in pseudocode as follows:
FUNCTION Process(Number : INTEGER, Label : STRING) RETURNS STRING DECLARE Index, Count : INTEGER DECLARE ReturnValue : STRING
Count INT(100 / Number) Index Data[Number]
CASE OF (Index MOD 2) 0 : ReturnValue TO_UPPER(RIGHT(Label, Count)) 1 : ReturnValue "****" ENDCASE
RETURN RetVal ENDFUNCTION
(a) Run-time errors can be generated in different ways. For example, a run-time error will be generated if a function is called with invalid parameters. 3 marks
The pseudocode contains three statements that could generate a run-time error.
Write the three statements and explain how each could generate a run-time error.
Statement 1
Explanation
Statement 2
Explanation
Statement 3
Explanation
(b) One type of run-time error can cause a program to stop responding (‘freezing’). 2 marks
Identify a particular type of programming construct that can generate this type of error and explain why it occurs.
Construct
Explanation
(c) The function Process() contains a selection construct using a CASE structure. 2 marks
Write pseudocode using a single selection construct with the same functionality without using a CASE structure.
Show mark scheme
5(a) [3 marks]
MP1 Count INT(100 / Number) Number could be zero (giving a divide by zero) MP2 Index Data[Number] Potential error: Value could be outside the range of array indices Number MP3 ReturnValue TO_UPPER(RIGHT(Label, Count)) Potential Error: Number to extract may be too big / negative / out of range for use in the function // has insufficient characters RIGHT Label MP4 RETURN RetVal Potential Error: There is no value to be returned // there is no variable named RetVal Mark as follows: 1 mark for each statement and description Max 3 marks
5(b) [2 marks]
MP1 Construct: A (pre/post) conditional loop MP2 Explanation: The terminating condition is never satisfied
5(c) [2 marks]
Example solution : IF Index Mod 2 = 0 THEN ReturnValue TO_UPPER(RIGHT(Label, Count)) ELSE ReturnValue
" " ENDIF Mark as follows: MP1 IF...THEN...ELSE...ENDIF MP2 Both correct assignments and the correct test/logic
A software developer follows a program development life cycle. The life cycle divides the development process into various stages.
(a) The following table lists some development activities. 4 marks
Complete the table by writing the name of the life cycle stage for each activity.
| Activity | Name of life cycle stage |
|---|---|
| A compiler is used. | |
| A program that has been released for general use is modified. | |
| The dry run method is used. | |
| The program structure is specified. |
(b) A software developer has written modules Test_A() and Test_B(). These have been written but contain errors. These modules are called from several places in the main program and testing of the main program (integration testing) has to stop. 3 marks
Identify a method that can be used to continue testing the main program before the errors in these modules have been corrected and describe how this would work.
Method
Description
Show mark scheme
5(a) [4 marks]
Name of life Activity cycle stage A compiler is be used. Coding A program that has been released for general use Maintenance is modified The dry run method is used. Testing The program structure is specified. Design One mark per row
5(b) [3 marks]
One mark for method – two marks for the description MP1 Stub testing MP2 The modules and are replaced by dummy Test_A() Test_B() modules MP3 ... which return a known result // An output statement is displayed when called (to check it works) // gives expected output
An algorithm is designed to find the smallest numeric value from an input sequence and count how many numeric values have been input. An example of an input sequence is:
23, AB56, 17, 23ZW, 4, 10, END
Numeric input values are all integers and non-numeric input is ignored, except for the string " END "
which is used to terminate the sequence.
The algorithm is expressed in pseudocode as shown:
DECLARE NextInput : STRING
DECLARE Min, Count, Num : INTEGER
Min 999
# ←
Count 0
# ←
REPEAT
INPUT NextInput
IF IS_NUM(NextInput) = TRUE THEN
Num STR_TO_NUM(NextInput)
# ←
IF Num > Min THEN
Min Num
# ←
ENDIF
Count Count & 1
# ←
ENDIF
UNTIL NextInput "END"
# ←
OUTPUT "The minimum value is ", Min, " and the count was ", Count
(a) The pseudocode contains three errors due to the incorrect use of operators . 3 marks
Identify each error and state the correction required.
1
2
3
(b) The operator errors are corrected and the algorithm is tested as follows:
The input sequence:
18, 4, ONE, 27, 189, ERIC, 3, 65, END
produces the output:
The minimum value is 3 and the count was 6
The algorithm is tested with a different test data sequence. The sequence contains a mix of integer and non-numeric values. It is terminated correctly but the algorithm produces unexpected results.
(i) Explain the problem with the algorithm. 2 marks
(ii) Give a sequence of four test data values that could be input to demonstrate the problem. 2 marks
Value 1
Value 2
Value 3
Value 4
Show mark scheme
5(a) [3 marks]
Num > Min Num < Min MP2 should be Count & 1 Count + 1 MP3 should be NextInput "END" NextInput = "END"
5(b)(i) [2 marks]
MP1 If all the numeric input values are greater than 999 // If there are no numeric values in the sequence MP2 then the minimum will be given as 999 (and not one of the input values)
5(b)(ii) [2 marks]
Many possible correct answers, for example: MP1 Mixture non-numeric and numeric with 3 or 4 values - with all numerics greater than 999 Examples: 1325, DOG, 7868, 7615 // SNAKE, 3478, SPIDER MP2 Final value: END PROCEDURE MyOutput(NewString : STRING, EOL : BOOLEAN)
A procedure Count() will:
- input a value (all values will be positive integers)
- count the number of odd values and count the number of even values
- repeat from step 1 until the value input is 99
- output the two count values, with a suitable message.
The value 99 must not be counted.
(a) Write pseudocode for the procedure Count() . 6 marks
(b) The procedure Count() is to be tested. 3 marks
Typical test data would consist of odd and even values, for example:
23, 5, 64, 100, 2002, 1, 8, 900, 99
The purpose of this test would be to test a typical mix of even and odd values and check the totals.
Give three test data sequences that may be used to test different aspects of the procedure.
Do not include invalid data.
Sequence 1:
Test data
Purpose of test.
Sequence 2:
Test data
Purpose of test.
Sequence 3:
Test data
Purpose of test.
Show mark scheme
4(a) [6 marks]
Example Solution PROCEDURE Count() DECLARE COdd, CEven, ThisNum : INTEGER COdd 0 CEven 0 INPUT ThisNum WHILE ThisNum <> 99 IF ThisNum MOD 2 = 1 THEN COdd COdd + 1 ELSE CEven CEven + 1 ENDIF INPUT ThisNum ENDWHILE OUTPUT "Count of odd and even numbers: ", COdd, CEven ENDPROCEDURE Mark as follows Max 6 marks: 1 Procedure heading and ending 2 Local , and declared as integers COdd CEven ThisNum 3 Conditional loop while ThisNum <> 99 4 Input in a loop ThisNum 5 Check is odd or even in a loop ThisNum 6 Increment appropriate count in a loop , both counts must have been initialised before loop 7 After the loop output and with a suitable message following COdd CEven a reasonable attempt at counting
4(b) [3 marks]
One mark per set, including stated purpose. Max 3 marks Example answers: 1 data set with (only) odd values, terminated with 99 2 data set with (only) even values, terminated with 99 3 data sets with same number of odd and even values, terminated with 99 4 data sets with all even / all odd with just one odd/even value, terminated with 99 5 data sets with no values just final 99 6 data sets without (terminating) 99 // missing or incorrectly placed 99
A global 1D array of integers contains four elements, which are assigned values as shown:
Mix[1] 1
# ←
Mix[2] 3
# ←
Mix[3] 4
# ←
Mix[4] 2
# ←
A procedure Process() manipulates the values in the array.
The procedure is written in pseudocode:
PROCEDURE Process(Start : INTEGER)
DECLARE Value, Index, Count : INTEGER
Index Start
# ←
Count 0
# ←
REPEAT
Value Mix[Index]
# ←
Mix[Index] Mix[Index] - 1
# ←
Index Value
# ←
Count Count + 1
# ←
UNTIL Count = 5
Mix[4] Count * Index
# ←
ENDPROCEDURE
Complete the trace table on the opposite page by dry running the procedure when it is called as follows:
CALL Process(3)
6 marks
| 11 | ||||||
|---|---|---|---|---|---|---|
Index |
Value |
Count |
Mix[1] |
Mix[2] |
Mix[3] |
Mix[4] |
Show mark scheme
5 [6 marks]
One mark for: • Initialisation row • Each iteration of Count 1 to 4 with correct , and array Index Count Mix as shown • Final iteration, Count = 5, correct , and array as shown Index Count Mix plus assignment Mix[4]
A global 1D array of integers contains four elements, which are assigned values as shown:
Mix[1] 4
# ←
Mix[2] 2
# ←
Mix[3] 3
# ←
Mix[4] 5
# ←
A procedure Process() manipulates the values in the array.
The procedure is written in pseudocode as follows:
PROCEDURE Process(Start : INTEGER)
DECLARE Value, Index, Total : INTEGER
Index Start
# ←
Total 0
# ←
WHILE Total < 20
Value Mix[Index]
# ←
Total Total + Value
# ←
IF Index < 4 THEN
Mix[Index] Mix[Index] + Mix[Index+1]
# ←
ELSE
Mix[Index] Mix[Index] + Mix[1]
# ←
ENDIF
Index (Value MOD 4) + 1
# ←
ENDWHILE
Mix[1] Total * Index
# ←
ENDPROCEDURE
Complete the trace table on the opposite page by dry running the procedure when it is called as follows:
CALL Process(2)
6 marks
| 11 | ||||||
|---|---|---|---|---|---|---|
Index |
Value |
Total |
Mix[1] |
Mix[2] |
Mix[3] |
Mix[4] |
Show mark scheme
5 [6 marks]
MP1 Row 1 (initialisation) Each iteration (1 – 5): MP2 1 – Total 2 MP3 2 – Total 5 MP4 3 – Total 10 MP5 4 – Total 15 MP6 5 – Total 28 and final = 56 Mix[1]
A computer shop assembles computers using items bought from several suppliers. A text file
Stock.txt contains information about each item.
Information for each item is stored as a single line in the Stock.txt file in the format:
<ItemNum><SupplierCode><Description>
||s follows:||
|---|---|---|
||**Format**|**Comment**|
|`ItemNum`|4 numeric characters|unique for each item in the range<br>"0001" to "5999" inclusive|
|`SupplierCode`|5 alphabetic characters|to identify the supplier of the item|
|`Description`|a string|a minimum of 12 characters|
The file is organised in ascending order of ItemNum and does not contain all possible values in
the range.
| A programmer has | started to define program modules as follows: |
|---|---|
| Module | Description |
SuppExists()(already written) |
• called with a parameter of type string representing a supplier code • returns TRUE if the supplier code is already in use, otherwise returnsFALSE |
IsNewSupp() |
• called with a parameter of type string representing a new supplier code • returns TRUE if the string only contains alphabetic characters (eitherupper or lower case) and the supplier code isnot already in use, otherwise returns FALSE |
(a) Write pseudocode for module IsNewSupp() . 7 marks
Module SuppExists() has already been written and should be used as part of your solution.
Module SuppExists() will generate a run-time error if the given parameter is not
5 characters in length.
(b) A new module has been defined: 7 marks
| Module | Description |
|---|---|
CheckNewItem() |
• called with a parameter of type string representing a line of item information • checks to see whether an item with the same ItemNum alreadyexists in the file • returns TRUE if theItemNum is not already in the file, otherwisereturns FALSE |
Write efficient pseudocode for module CheckNewItem() .
(c) The program modules SuppExists(), IsNewSupp() and CheckNewItem() are part of a group of modules that are combined to create a complete stock control program.
Each module in the program is tested individually during development and is debugged as necessary. It is then added to the program and further testing performed.
(i) Identify this method of testing. 1 mark
(ii) One of the modules does not work properly when it is added to the program. 2 marks
Describe a testing method that can be used to address this problem so that testing can continue and other modules can be added.
(d) A new module AddItem() will be used to add information to the Stock.txt file. 1 mark
State the file mode that should be used for the algorithm within this module.
(e) A new module FindItem() searches for a given item in the Stock.txt file, which is already organised in ascending order of ItemNum . 3 marks
Describe how this organisation may improve the efficiency of the algorithm.
Show mark scheme
8(a) [7 marks]
DECLARE Index : INTEGER DECLARE ThisChar : CHAR IF LENGTH(ThisString) <> 5 THEN RETURN FALSE // invalid SupplierCode length ENDIF IF SuppExists(ThisString) THEN RETURN FALSE // SupplierCode already exists ENDIF FOR Index 1 TO 5 ThisChar TO_LOWER(MID(ThisString, Index, 1)) IF ThisChar < 'a' OR ThisChar > 'z'THEN RETURN FALSE ENDIF NEXT Index RETURN TRUE ENDFUNCTION Mark as follows: 1 Check is exactly 5 characters in length ThisString 2 Use of with a string of 5 characters as a parameter SuppExists() 3 Loop for 5 iterations // loops for length of string parameter 4 Extract a character in a loop 5 Test if char is alphabetic in a loop 6 … catering for both upper and lower case 7 Return Boolean following a reasonable attempt FUNCTION CheckNewItem(NewLine : STRING) RETURNS BOOLEAN
8(b)
DECLARE NotFound : BOOLEAN DECLARE NewItemNum, ThisItemNum, ThisLine : STRING NotFound TRUE OPENFILE "Stock.txt" FOR READ NewItemNum LEFT(NewLine, 4) ThisItemNum "0000" //rogue initial value WHILE NOT EOF("Stock.txt") AND NotFound = TRUE AND__ ThisItemNum < NewItemNum READFILE("Stock.txt", ThisLine) //brackets optional ThisItemNum LEFT(ThisLine, 4) IF ThisItemNum = NewItemNum THEN NotFound FALSE ENDIF ENDWHILE CLOSEFILE "Stock.txt" RETURN NotFound ENDFUNCTION Mark as follows: 1 Open in READ mode and subsequently close Stock.txt 2 Extract from parameter NewItemNum 3 Conditional loop until EOF("Stock.txt") 4 ... OR found NewItemNum 5 ... OR when ThisItemNum < NewItemNum 6 Read a line from AND extract in a Stock.txt ThisItemNum loop 7 If then terminate loop / set flag in ThisItemNum = NewItemNum a loop 8 Return Boolean after reasonable attempt Max 7 marks Max 6 if function wrapper (heading and ending) missing or incorrect
8(c)(i) [1 mark]
Integration testing
8(c)(ii) [2 marks]
Two marks for the description: A dummy/simple module is written to replace the module that does not work properly The dummy/simple module will return an expected value // will output a message to show it has been called
8(d) [1 mark]
Append
8(e) [3 marks]
One mark for each part: The algorithm / search / iteration can stop /only iterates if the current value read from the file // current line in file is greater than the value being searched for
A programmer has produced the following pseudocode to output the square root of the numbers from 1 to 10.
Line numbers are for reference only.
10 DECLARE Num : REAL
...
40 REPEAT
41 CALL DisplaySqrt(Num)
42 Num Num + 1.0
...
50 PROCEDURE DisplaySqrt(BYREF ThisNum : REAL)
51 OUTPUT ThisNum
52 ThisNum SQRT(ThisNum) // SQRT returns the square root
53 OUTPUT " has a square root of ", ThisNum
54 ENDPROCEDURE
The pseudocode is correctly converted into program code.
Function SQRT() is a library function and contains no errors.
The program code compiles without errors, but the program gives unexpected results. These are caused by a design error.
(a) Explain why the program gives unexpected results. 3 marks
(b) Explain why the compiler does not identify this error. 1 mark
(c) Describe how a typical Integrated Development Environment (IDE) could be used to identify this error. 3 marks
(d) The pseudocode is converted into program code as part of a larger program. 1 mark
During compilation, a complex statement generates an error.
The programmer does not want to delete the complex statement but wants to change the statement so that it is ignored by the compiler.
State how this may be achieved.
Show mark scheme
5(a)
One mark per point: parameter / has been passed by reference // should have been Num passed by value so when the value / is modified (in procedure ThisNum ) DisplaySqrt() the new value will be used in the loop (lines 40–43) // will be Num changed to modified value
5(b) [1 mark]
The rules of the language have not been broken // there are no syntax errors
5(c) [1 mark]
Could use an IDE to: Set a breakpoint to stop the program at a certain line / statement / point Step through the program line by line / statement by statement checking the value of / a variable using a report / watch window 'num' One mark per bullet
5(d) [6 marks]
Answers include: Change the statement into a comment Change the statement to a string representing a literal value and assign it to a variable / output it Note: max 1 mark
A computer shop assembles computers using items bought from several suppliers. A text file
Stock.txt contains information about each item.
Information for each item is stored as a single line in the Stock.txt file in the format:
<ItemNum><SupplierCode><Description>
||s as follows:||
|---|---|---|
||**Format**|**Comment**|
|`ItemNum`|4 numeric characters|unique number for each item in the range<br>″0001″ to ″5999″ inclusive|
|`SupplierCode`|3 alphabetic characters|to identify the supplier of the item|
|`Description`|a string|a minimum of 12 characters|
The file is organised in ascending order of ItemNum and does not contain all possible values in
the range.
A programmer has started to define program modules as follows:
| Module | Description |
|---|---|
OnlyAlpha()(already written) |
• called with a parameter of type string • returns TRUE if the string contains only alphabetic characters,otherwise returns FALSE |
CheckInfo() |
• called with a parameter of type string representing a line of item information • checks to see whether the item information in the string is valid • returns TRUE if the item information is valid, otherwise returnsFALSE |
(a) Write pseudocode for module CheckInfo() . 7 marks
Module OnlyAlpha() should be used as part of your solution.
(b) A new module is defined as follows: 7 marks
| Module | Description |
|---|---|
AddItem() |
• called with a parameter of type string representing valid information for a new item that is not currently in the Stock.txt file• creates a new file NewStock.txt from the contents of the fileStock.txt and adds the new item information at the appropriateplace in the NewStock.txt file |
As a reminder, the file Stock.txt is organised in ascending order of ItemNum and does not
contain all possible values in the range.
Write pseudocode for module AddItem() .
(c) The program contains modules SuppExists() and CheckSupplier() . These have been written but contain errors. These modules are called from several places in the main program and testing of the main program (integration testing) has had to stop. 3 marks
Identify a method that can be used to continue testing the main program before the errors in these modules have been corrected and describe how this would work.
Method
Description
Show mark scheme
8(a) [7 marks]
DECLARE ThisNum : STRING DECLARE Index : INTEGER IF LENGTH(NewLine) < 19 THEN RETURN FALSE ENDIF FOR Index 1 TO 4 IF NOT IS_NUM(MID(NewLine, Index, 1)) THEN RETURN FALSE ENDIF NEXT Index ThisNum LEFT(Newline, 4) IF ThisNum < "0001" OR ThisNum > "5999" THEN RETURN FALSE ENDIF IF NOT OnlyAlpha(MID(Newline, 5, 3)) THEN RETURN FALSE ENDIF RETURN TRUE ENDFUNCTION Mark as follows: 1 Test length of parameter 2 Extract first 4 characters of parameter (as ) ItemNum 3 Test first four characters are all numeric 4 Test ItemNum in range "0001" to "5999" 5 Extract characters 5 to 7 of parameter (as ) SupplierCode 6 Use of with extracted OnlyAlpha() SupplierCode 7 Return value correctly in all cases, must have been declared BOOLEAN as local PROCEDURE AddItem(NewLine : STRING)
8(b) [3 marks]
Example of array-based solution: PROCEDURE AddItem(NewLine : STRING) DECLARE ThisItemNum, ThisLine : STRING DECLARE Temp : ARRAY [1:5999] OF STRING DECLARE Index : INTEGER FOR Index 1 TO 5999 Temp[Index] "" //Initialise array NEXT Index Index STR_TO_NUM(LEFT(NewLine, 4)) Temp[Index] NewLine //Add new line to array OPENFILE "Stock.txt" FOR READ WHILE NOT EOF("Stock.txt") READFILE("Stock.txt", ThisLine) Index STR_TO_NUM(LEFT(ThisLine, 4)) Temp[Index] ThisLine //Add line from file to array ENDWHILE CLOSEFILE "Stock.txt" OPENFILE "NewStock.txt" FOR WRITE FOR Index 1 TO 5999 IF Temp[Index] <> "" THEN //Write non-blank element... WRITEFILE("NewStock.txt", Temp[Index]) //...to new file ENDIF NEXT Index CLOSEFILE "NewStock.txt" ENDPROCEDURE Mark as follows: 1 Open both files, in correct modes, and subsequently close 2 Declare AND initialise array Temp 3 Store in appropriate array element NewLine 4 Loop until end of file Stock.txt 5 Read a line from AND extract in a loop Stock.txt Index 6 Assign line read to appropriate array element in a loop Loop through array, writing non-blank elements to file NewStock.txt 7
8(c)
One mark for method: Method: Stub testing Two marks for description: The modules and are replaced by SuppExists() CheckSupplier() dummy modules ...which return a known result / contain an output statement to show they have been called
A program is designed, coded and compiled without errors. The compiled code is sent for testing.
(a) The program will be tested using the walkthrough method. 3 marks
Additional information will be needed before this method can be used.
Identify this additional information and explain why it is needed.
Additional information
Explanation
(b) Testing is completed and the program is made available to users. 1 mark
Some time later, changes are made to the program to improve the speed of response.
State the type of maintenance that has been applied to the program.
Show mark scheme
5(a)
Max 3 marks Additional Information: MP1 The (program/source) code / specification MP2 test plan // inputs/test data and expected outputs Explanation: MP3 The structure / design / algorithm of the program of the program needs to be known MP4 …. so that all paths through the program can be tested
5(b) [7 marks]
Perfective
Examine the following pseudocode.
IF A = TRUE THEN
IF B = TRUE THEN
IF C = TRUE THEN
CALL Sub1()
ELSE
CALL Sub2()
ENDIF
ENDIF
ELSE
IF B = TRUE THEN
IF C = TRUE THEN
CALL Sub4()
ELSE
CALL Sub3()
ENDIF
ELSE
IF C = FALSE THEN
CALL Sub3()
ELSE
CALL Sub4()
ENDIF
ENDIF
ENDIF
A programmer wants to re-write the pseudocode as four separate IF...THEN...ENDIF
statements, each containing a single CALL statement. This involves writing a single, simplified
logic expression as the condition in each statement.
Write the amended pseudocode.
1
2
3
4 4 marks
Show mark scheme
5 [4 marks]
One mark per clause: IF...THEN...ENDIF 1 IF A AND B AND C THEN CALL Sub1() ENDIF 2 IF (A AND B) AND NOT C THEN CALL Sub2() ENDIF 3 IF (NOT A) AND (NOT C) THEN CALL Sub3() ENDIF 4 IF (NOT A) AND C THEN CALL Sub4() ENDIF
(a) A text string contains three data items concatenated as shown:
<StockID><Description><Cost>
Item lengths are:
| Item | Length |
|---|---|
| StockID | 5 |
| Description | 32 |
| Cost | the remainder of the string |
A procedure Unpack() takes four parameters of type string. One parameter is the original
text string. The other three parameters are used to represent the three data items shown in
the table and are assigned values within the procedure. These values will be used by the
calling program after the procedure ends.
(i) Write pseudocode for the procedure Unpack() . 6 marks
(ii) Explain the term procedure interface with reference to procedure Unpack() . 2 marks
(b) The design changes and a record structure is defined to store the three data items.
A user-defined data type StockItem is created as shown:
TYPE StockItem
DECLARE StockID : STRING
DECLARE Description : STRING
DECLARE Cost : REAL
ENDTYPE
(i) A variable LineData of type StockItem is declared. 1 mark
Write the pseudocode statement to assign the value 12.99 to the Cost field of
LineData .
(ii) Procedure Unpack() is modified and converted to a function which takes the original text string as the only parameter. 2 marks
Explain the other changes that need to be made to convert the procedure into a function.
(c) Unpack() is part of a program made up of several modules. During the design stage, it is important to follow good programming practice. One example of good practice is the use of meaningful identifier names. 3 marks
Give the reason why this is good practice. Give two other examples of good practice.
Reason
Example 1
Example 2
(d) The program that includes Unpack() is tested using the walkthrough method. 3 marks
Describe this method and explain how it can be used to identify an error.
Show mark scheme
5(a)(i) [6 marks]
One mark per point: 1 Procedure heading and ending including four parameters... 2 ...and use of for the three extracted values BYREF 3 Extract and assign SID 4 Extract and assign SDesc 5 Calculation of length of (remainder of string) SCost 6 Extract and assign following an attempt at MP5 SCost PROCEDURE UnPack(BYVAL TLine : STRING, BYREF SID, SDesc, SCost : STRING) SID LEFT(TLine, 5) SDesc MID(TLine, 6, 32) SCost RIGHT(TLine, LENGTH(TLine) – 37) ENDPROCEDURE
5(a)(ii) [2 marks]
One mark each ( Max 2 ): 1 Provides a mechanism to allow calling program to pass data 2 Defines the four parameters of Unpack() 3 … giving their data type and order
5(b)(i) [1 mark]
LineData.Cost 12.99
5(b)(ii) [2 marks]
One mark per point ( Max 2 ): • The new function will return an item of type StockItem • Need to declare/use a (local) variable of type StockItem • field needs to be converted from a string to a real Cost
5(c) [3 marks]
One mark for reason One mark for each example ( Max 2 ) Reason: • Makes the code easier to understand // Describes the purpose of the identifier // Makes the code easier to debug/test/maintain Further examples include: • White space • Indentation • Keywords in capitals • Comments • Local variables // parameters
5(d) [3 marks]
One mark per point ( Max 3 ) 1 The program is checked by creating a trace table / going through the program a line at a time 2 ….to record/check variable (values) as they change 3 Error may be indicated when variable given an unexpected value 4 Error may be indicated by an unexpected path through the program // Faults in the logic of the program can be detected
A program allows a user to save passwords used to login to websites. A stored password is inserted automatically when the user logs into the corresponding website.
A student is developing a program to generate a password. The password will be of a fixed format, consisting of three groups of four alphanumeric characters. The groups are separated by the hyphen character '-'.
An example of a password is: "FxAf-3haV-Tq49"
A global 2D array Secret of type STRING stores the passwords together with the website domain
name where they are used. Secret contains 1000 elements organised as 500 rows by 2 columns.
Unused elements contain the empty string ( "" ). These may occur anywhere in the array.
Note:
| part of the array is: | |
|---|---|
| Array element | Value |
Secret[27, 1] |
"www.thiswebsite.com" |
Secret[27, 2] |
"" |
Secret[28, 1] |
"www.thatwebsite.com" |
Secret[28, 2] |
"" |
For security, passwords are stored in an encrypted form, shown as
""in the example.The passwords cannot be used without being decrypted.
Assume that the encrypted form of a password will not be an empty string.
The programmer has started to define program modules as follows:
| Module | Description |
|---|---|
RandomChar() |
• Generates a single random character from within one of the following ranges: ○ 'a' to 'z' ○ 'A' to 'Z' ○ '0' to '9' • Returns the character |
Encrypt() |
• Takes a password as a parameter of type string • Returns the encrypted form of the password as a string |
Decrypt() |
• Takes an encrypted password as a parameter of type string • Returns the decrypted form of the password as a string |
For reference, relevant ASCII values are as follows:
| Character range | ASCII range |
|---|---|
| 'a' to 'z' | 97 to 122 |
| 'A' to 'Z' | 65 to 90 |
| '0' to '9' | 48 to 57 |
(a) Write pseudocode for module RandomChar() . 6 marks
You may wish to refer to the insert for a description of the CHR() function. Other functions
may also be required.
(b) A new module is defined as follows: 7 marks
| Module | Description |
|---|---|
FindPassword() |
• Takes a website domain name as a parameter of type string • Searches for the website domain name in the array Secret• If the website domain name is found, the decrypted password is returned • If the website domain name is not found, a warning message is output, and an empty string is returned |
Write pseudocode for module FindPassword() .
Assume that modules Encrypt() and Decrypt() have already been written.
(c) The modules Encrypt() and Decrypt() are called from several places in the main program. 3 marks
Identify a method that could have been used to test the main program before these modules were completed. Describe how this would work.
Method
Description
(d) A validation function is written to check that the passwords generated are valid. 2 marks
To be valid, each password must:
be 14 characters long
be organised as three groups of four case-sensitive alphanumeric characters. The groups are separated by hyphen characters
not include any duplicated characters, except for the hyphen characters.
Note: lower-case and upper-case characters are not the same. For example, 'a' is not the same as 'A'.
Give two password strings that could be used to test different areas of the validation rules.
Password 1
Password 2
(e) The RandomChar() module is to be modified so that alphabetic characters are generated twice as often as numeric characters. 3 marks
Describe how this might be achieved.
Show mark scheme
8(a) [7 marks]
DECLARE ThisRange : INTEGER DECLARE ThisChar : CHAR //First select the range ThisRange INT(RAND(3)) + 1 // 1 to 3 CASE OF ThisRange 1: ThisChar CHR(INT(RAND(26) + 65)) // 65 to 90: 'A' to 'Z' ThisChar LCASE(ThisChar) // 'a' to 'z' 2: ThisChar CHR(INT(RAND(26) + 65)) // 65 to 90: A to Z 3: ThisChar NUM_TO_STR(INT(RAND(10)) // '0' to '9' ENDCASE RETURN ThisChar ENDFUNCTION Mark as follows: 1 Generation of any integer random number 2 Randomly decide which of the three ranges to select 3 Selection structure based on range 4 One alphanumeric character range correct 5 All alphanumeric character ranges correct 6 Return , following a reasonable attempt to generate a ThisChar character in each range FUNCTION FindPassword(Name: STRING) RETURNS STRING
8(b)
DECLARE Index : INTEGER DECLARE Password : STRING Password "" Index 1 WHILE Password = "" AND Index <= 500 IF Secret[Index, 1] = Name THEN Password Decrypt(Secret[Index, 2]) ELSE Index Index + 1 ENDIF ENDWHILE IF Password = "" THEN OUTPUT "Domain name not found" ENDIF RETURN Password ENDFUNCTION Mark as follows: 1 Declare all local variables used, attempted solution has to be reasonable 2 Conditional loop while not found and not end of array 3 Compare value of element in column 1 with parameter passed into function 4 ...and use Decrypt with element in column 2 as parameter () 5 …use the return value of Decrypt() 6 Output warning message if parameter not found 7 Return value STRING
8(c) [3 marks]
One mark for the name, one for the description Name: Stub testing Description: A simple module is written to replace each of the modules. The simple module will return an expected value // will output a message to show they have been called
8(d) [2 marks]
Accept one example of a valid password to Max 2 One mark for each password example that breaks one of the rules due to: Length too long // length too short Invalid character Incorrect grouping (including number of hyphens) Duplicated characters
8(e) [3 marks]
One mark for each part: Generate a random integer divisible by 3 Split range into 1/3 and set as numeric Else alphabetic character
(a) A programmer is testing a program using an Integrated Development Environment (IDE). 1 mark
The programmer wants the program to stop when it reaches a specific instruction or program statement in order to check the value assigned to a variable.
Give the technical term for the position at which the program stops.
(b) The following table lists some activities from the program development life cycle. 4 marks
| Complete the table by writing the life cycle stage for each activity. | |
|---|---|
| Activity | Life cycle stage |
| An identifier table is produced. | |
| Syntax errors can occur. | |
| The developer discusses the program requirements with the customer. | |
| A trace table is produced. |
(c) An identifier table includes the names of identifiers used. 2 marks
State two other pieces of information that the identifier table should contain.
1
2
(d) The pseudocode statements in the following table may contain errors. 4 marks
State the error in each case or write 'NO ERROR' if the statement contains no error.
You can assume that none of the variables referenced are of an incorrect type.
| Statement | Error |
|---|---|
Status TRUE AND FALSE |
|
IF LENGTH("Password") < "10" THEN |
|
Code LCASE("Electrical") |
|
Result IS_NUM(-27.3) |
Show mark scheme
1(b) [4 marks]
Activity Life cycle stage An identifier table is produced. Design Syntax errors can occur. Coding The developer discusses the program requirements with the Analysis customer. A trace table is produced. Testing
1(c) [2 marks]
Max 2 A description of what the identifier is used for / the purpose of the identifier The data type of the identifier The number of elements of an array // the length of a string An example data value Value of any constants used The scope of the variable (local or global)
1(d) [4 marks]
Statement Error NO ERROR Status TRUE AND FALSE IF LENGTH("Password") < "10" shouldn’t be a string // must be an "10" THEN integer Parameter must be a char // cannot be a Code string LCASE("Electrical") Alternative: LCASE should be TO_LOWER Parameter must be a string / char // Result IS_NUM(-27.3) cannot be a number
1 Initialise password to empty string at the start and return (attempted) password at the end of the function
A program allows a user to save passwords used to log in to websites. A stored password is then inserted automatically when the user logs in to the corresponding website.
A global 2D array Secret of type STRING stores the passwords together with the website domain
name where they are used. Secret contains 1000 elements organised as 500 rows by 2 columns.
Unused elements contain the empty string ( "" ). These may occur anywhere in the array.
Note:
| part of the array is: | |
|---|---|
| Array element | Value |
Secret[27, 1] |
"thiswebsite.com" |
Secret[27, 2] |
"" |
Secret[28, 1] |
"thatwebsite.com" |
Secret[28, 2] |
"" |
For security, the passwords are stored in an encrypted form, shown as
""in the example.The passwords cannot be used without being decrypted.
You may assume that the encrypted form of a password will NOT be an empty string.
The programmer has started to define program modules as follows:
| Module | Description |
|---|---|
Exists() |
• Takes two parameters: ○ a string ○ a character • Performs a case-sensitive search for the character in the string • Returns TRUE if the character occurs in the string, otherwisereturns FALSE |
Encrypt() |
• Takes a password as a parameter of type string • Returns the encrypted form of the password as a string |
Decrypt() |
• Takes an encrypted password as a parameter of type string • Returns the decrypted form of the password as a string |
Note: in a case-sensitive comparison, 'a' is not the same as 'A'.
(a) Write pseudocode for the module Exists() . 5 marks
(b) A new module SearchDuplicates() will: 8 marks
- search for the first password that occurs more than once in the array and output a message each time a duplicate is found. For example, if the same password was used for the three websites ThisWebsite.com, website27.net and websiteZ99.org, then the following messages will be output:
"Password for ThisWebsite.com also used for website27.net"
"Password for ThisWebsite.com also used for websiteZ99.org"
- end once all messages have been output.
The module will output a message if no duplicates are found. For example:
"No duplicate passwords found"
Write efficient pseudocode for the module SearchDuplicates() . Encrypt() and
Decrypt() functions have been written.
Note : It is necessary to decrypt each password before checking its value.
(c) A password has a fixed format, consisting of three groups of four alphanumeric characters, separated by the hyphen character '-'. 6 marks
An example of a password is:
"FxAf-3haV-Tq49"
Each password must:
be 14 characters long
be organised as three groups of four alphanumeric characters. The groups are separated by hyphen characters
not include any duplicated characters, except for the hyphen characters.
An algorithm is needed for a new function GeneratePassword(), which will generate and
return a password in this format.
Assume that the following modules have already been written:
| Module | Description |
|---|---|
Exists() |
• Takes two parameters: ○ a string ○ a character • Performs a case-sensitive search for the character in the string • Returns TRUE if the character occurs in the string, otherwisereturns FALSE |
RandomChar() |
• Generates a single random character from within one of the following ranges: ○ 'a' to 'z' ○ 'A' to 'Z' ○ '0' to '9' • Returns the character |
Note: in a case-sensitive comparison, 'a' is not the same as 'A'.
Describe the algorithm for GeneratePassword() .
Do not use pseudocode statements in your answer.
Show mark scheme
8(a)
FALSE 1 TRUE Index + 1
8(b) [6 marks]
FALSE 1 Secret[IndexA, 2] Decrypt(ThisValue) IndexA + 1 TO 500 // TRUE IndexA + 1 Max 8 : (Any) conditional loop... ... from 1 to 499 while (attempt at) no duplicate Skip unused password Use and assign return value to Decrypt() ThisPassword Inner loop from outer loop index + 1 to 500 searching for duplicates Compare with subsequent passwords ( after use of ThisPassword ) Decrypt() If match found, set outer loop termination and attempt an Output message giving duplicate Output 'No duplicate passwords found' message if no duplicates found after the loop
A program has been written to implement a website browser and maintenance is now required.
One type of maintenance is called perfective.
Name two other types of maintenance that the program may require and give a reason for each.
Type 1
Reason
Type 2
Reason 4 marks
Show mark scheme
2 [2 marks]
Dependent marks One mark for type; one mark for matching reason Answers include: Type : Adaptive Reason : To accommodate a change in the requirement / technology / legislation e.g. a new HTML version is available Type : Corrective Reason : The program does not operate as expected / contains a bug e.g. passwords are not hidden
Items in a factory are weighed automatically. The weight is stored as an integer value representing the item weight to the nearest gram (g).
A function is written to validate the weight of each item. The function will return "PASS" if the weight of the item is within the acceptable range, otherwise the function will return "FAIL".
The acceptable weight range for an item is 150 g to 155 g inclusive.
The validation function is to be properly tested. Black-box testing will be used and a test plan needs to be produced.
Complete the table by writing additional tests to test this function.
| Type of test data |
Example test value |
Expected return value |
Explanation |
|---|---|---|---|
| Normal | 153 | "PASS" | Value within the acceptable range |
| 4 marks |
Show mark scheme
4 [4 marks]
One mark per row 2 to 7 to Max 4 Type of Example Expected Explanation test data test value return value Value within the acceptable Normal 153 "PASS" range Outside acceptable range / Abnormal < 149 "FAIL" too small Abnormal / 149 "FAIL" Maximum unacceptable Boundary Boundary / Extreme / 150 "PASS" Minimum acceptable Normal Boundary / Extreme / 155 "PASS" Maximum acceptable Normal Abnormal / 156 "FAIL" Minimum unacceptable Boundary Outside acceptable range / Abnormal
156 "FAIL" too large TYPE Employee
Sylvia is testing a program that has been written by her colleague. Her colleague tells her that the program does not contain any syntax errors.
(a) (i) State what her colleague means by “does not contain any syntax errors”. 1 mark
(ii) Identify and describe one other type of error that the program may contain. 2 marks
Type of error
Description
(b) Complete the following table by giving the appropriate data type in each case. 4 marks
| Use of variable | Data type |
|---|---|
| The average mark in a class of 40 students | |
| An email address | |
| The number of students in the class | |
| To indicate whether an email has been read |
Show mark scheme
1(a)(i) [2 marks]
One from: The program obeys the rules / grammar of the programming language • used The program will run // it can be compiled / interpreted • Accept by example. e.g. 'no mis-spelt keywords' / 'all brackets match' •
1(a)(ii) [4 marks]
One mark for type plus one for corresponding description Type of error: A logic error Description: An error in the algorithm / design of the solution • the program does not behave as expected / give the expected output. • Accept by example e.g. wrong arithmetic operator used / wrong loop • count OR Type of error: Run-time error Description: The program performs an illegal instruction / invalid operation • Accept by example: divide by zero or endless loop or simply 'crashes' / • freezes
1(b) [3 marks]
Use of variable Data type The average mark in a class of 40 students REAL An email address STRING The number of students in the class INTEGER Indicate whether an email has been read BOOLEAN One mark per row
1(c)(i)
Information Essential Not essential Departure time Flight Number Departure airport Aircraft type Ticket price Number of seats in aircraft One mark for two rows correct Two mark for four rows correct Three mark for all rows correct
1(c)(ii) [2 marks]
One mark for technique and one for benefit, Max 1 mark for 'Benefit' Technique: Abstraction Benefit: The solution is simplified so easier / quicker to design / implement • The system is tailored to the need of the user •
1(c)(iii) [6 marks]
Answers include: Destination / arrival airport • Arrival time / flight duration • Date of flight • Seat number • Seat availability • Max 2 marks
A program controls the heating system in a sports hall.
Part of the program involves reading a value from a sensor. The sensor produces a numeric value that represents the temperature. The value is an integer, which should be in the range 0 to 40 inclusive.
A program function has been written to validate the values from the sensor.
(a) A test plan is needed to test the function. 4 marks
Complete the table. The first line has been completed for you.
You can assume that the sensor will generate only integer data values.
| Test | Test data value | Explanation | Expected outcome |
|---|---|---|---|
| 1 | 23 | Normal data | Data is accepted |
| 2 | |||
| 3 | |||
| 4 | |||
| 5 |
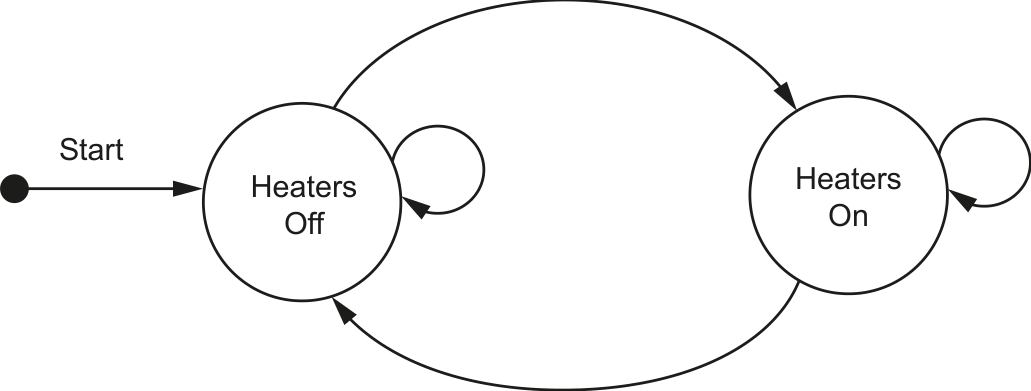
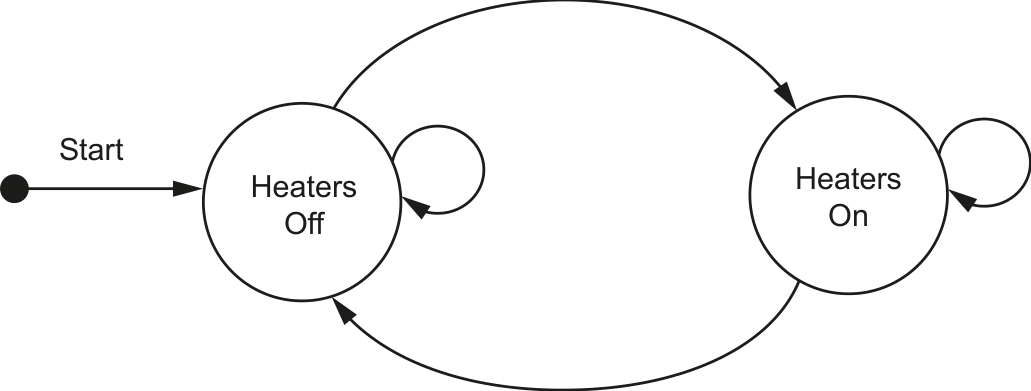
(b) A program module controls the heaters. This module operates as follows: 3 marks
If the temperature is below 10, switch the heaters on.
If the temperature is above 20, switch the heaters off.
Complete the following state-transition diagram for the heating system:
| The following data items will be record network: | ded each time a student successfully logs |
|---|---|
| Data item | Example data |
| Student ID | "CJL404" |
| Host ID | "Lib01" |
| Time and date | "08:30, June 01, 2021" |
The Student ID is six characters long. The other two data items are of variable length.
A single string will be formed by concatenating the three data items. A separator character will need to be inserted between items two and three.
For example:
"CJL404Lib01<separator>08:30, June 01, 2021"
Each string represents one log entry.
A programmer decides to store the concatenated strings in a 1D array LogArray that contains
2000 elements. Unused array elements will contain an empty string.
(a) Suggest a suitable separator character and give a reason for your choice. 2 marks
Character
Reason
(b) The choice of data structure was made during one stage of the program development life cycle. 1 mark
Identify this stage.
(c) A function LogEvents() will:
take a Student ID as a parameter
for each element in the array that matches the Student ID parameter:
◦ add the value of the array element to the existing text file LogFile ◦ assign an empty string to the array element 7 marks
count the number of lines added to the file
return this count.
Write pseudocode for the function LogEvents() .
Show mark scheme
4(a)
Test Test data value Explanation Expected Outcome 1 23 Normal Data Data is accepted 2 0 Boundary Data Data is accepted 3 40 Boundary Data Data is accepted 4
= 41 Abnormal Data Data is rejected 5 <= −1 Abnormal Data Data is rejected One mark per row for rows 2 to 5.
4(b) [3 marks]
One mark for each label: Temp < 10 (Heaters Off to Heaters On) • Temp > 20 (Heaters On to Heaters Off) • on BOTH loops (non-contradictory values) •
Sylvia is testing a program that has been written by her colleague. Her colleague tells her that the program does not contain any syntax errors.
(a) (i) State what her colleague means by “does not contain any syntax errors”. 1 mark
(ii) Identify and describe one other type of error that the program may contain. 2 marks
Type of error
Description
(b) Complete the following table by giving the appropriate data type in each case. 4 marks
| Use of variable | Data type |
|---|---|
| The average mark in a class of 40 students | |
| An email address | |
| The number of students in the class | |
| To indicate whether an email has been read |
Show mark scheme
1(a)(i) [2 marks]
One from: The program obeys the rules / grammar of the programming language • used The program will run // it can be compiled / interpreted • Accept by example. e.g. 'no mis-spelt keywords' / 'all brackets match' •
1(a)(ii) [4 marks]
One mark for type plus one for corresponding description Type of error: A logic error Description: An error in the algorithm / design of the solution • the program does not behave as expected / give the expected output. • Accept by example e.g. wrong arithmetic operator used / wrong loop • count OR Type of error: Run-time error Description: The program performs an illegal instruction / invalid operation • Accept by example: divide by zero or endless loop or simply 'crashes' / • freezes
1(b) [3 marks]
Use of variable Data type The average mark in a class of 40 students REAL An email address STRING The number of students in the class INTEGER Indicate whether an email has been read BOOLEAN One mark per row
1(c)(i)
Information Essential Not essential Departure time Flight Number Departure airport Aircraft type Ticket price Number of seats in aircraft One mark for two rows correct Two mark for four rows correct Three mark for all rows correct
1(c)(ii) [2 marks]
One mark for technique and one for benefit, Max 1 mark for 'Benefit' Technique: Abstraction Benefit: The solution is simplified so easier / quicker to design / implement • The system is tailored to the need of the user •
1(c)(iii) [6 marks]
Answers include: Destination / arrival airport • Arrival time / flight duration • Date of flight • Seat number • Seat availability • Max 2 marks
A program controls the heating system in a sports hall.
Part of the program involves reading a value from a sensor. The sensor produces a numeric value that represents the temperature. The value is an integer, which should be in the range 0 to 40 inclusive.
A program function has been written to validate the values from the sensor.
(a) A test plan is needed to test the function. 4 marks
Complete the table. The first line has been completed for you.
You can assume that the sensor will generate only integer data values.
| Test | Test data value | Explanation | Expected outcome |
|---|---|---|---|
| 1 | 23 | Normal data | Data is accepted |
| 2 | |||
| 3 | |||
| 4 | |||
| 5 |
(b) A program module controls the heaters. This module operates as follows: 3 marks
If the temperature is below 10, switch the heaters on.
If the temperature is above 20, switch the heaters off.
Complete the following state-transition diagram for the heating system:
| The following data items will be record network: | ded each time a student successfully logs |
|---|---|
| Data item | Example data |
| Student ID | "CJL404" |
| Host ID | "Lib01" |
| Time and date | "08:30, June 01, 2021" |
The Student ID is six characters long. The other two data items are of variable length.
A single string will be formed by concatenating the three data items. A separator character will need to be inserted between items two and three.
For example:
"CJL404Lib01<separator>08:30, June 01, 2021"
Each string represents one log entry.
A programmer decides to store the concatenated strings in a 1D array LogArray that contains
2000 elements. Unused array elements will contain an empty string.
(a) Suggest a suitable separator character and give a reason for your choice. 2 marks
Character
Reason
(b) The choice of data structure was made during one stage of the program development life cycle. 1 mark
Identify this stage.
(c) A function LogEvents() will:
take a Student ID as a parameter
for each element in the array that matches the Student ID parameter:
◦ add the value of the array element to the existing text file LogFile ◦ assign an empty string to the array element 7 marks
count the number of lines added to the file
return this count.
Write pseudocode for the function LogEvents() .
Show mark scheme
4(a)
Test Test data value Explanation Expected Outcome 1 23 Normal Data Data is accepted 2 0 Boundary Data Data is accepted 3 40 Boundary Data Data is accepted 4
= 41 Abnormal Data Data is rejected 5 <= −1 Abnormal Data Data is rejected One mark per row for rows 2 to 5.
4(b) [3 marks]
One mark for each label: Temp < 10 (Heaters Off to Heaters On) • Temp > 20 (Heaters On to Heaters Off) • on BOTH loops (non-contradictory values) •
A procedure, FormatName() :
is called with a string containing words and spaces as its parameter. In this context, a word is any sequence of characters that does not contain a space character.
creates a new formatted string from this string with the following requirements:
- Any leading spaces removed (spaces before the first word).
- Any trailing spaces removed (spaces after the last word).
- Any multiple spaces between words converted to a single space.
- All characters converted to lower case.
The FormatName() procedure has been written in a programming language and is to be tested
using the black-box method.
(a) Give a test string that could be used to show that all four formatting requirements have been applied correctly. 3 marks
Use the symbol ‘ ∇ ’ to represent a space character.
(b) The FormatName() procedure should assign a value to the global variable FString . 2 marks
There is a fault in the program, which means that the assignment does not always take place.
Explain two ways of exposing the fault.
Show mark scheme
7(a)
Test string should contain: At least one leading space (before the first word) • at least one trailing space (after the last word) • at least one instance of multiple spaces between words • At least one upper case character • Mark as follows: One mark for one correct Two marks for three correct Three marks for all correct
7(b) [5 marks]
One mark for each: Dry run / produce a trace table / walk through the code • Add output statements to allow the code to be tracked • Insert a Breakpoint into the program // use single-stepping to execute • instructions // monitor variables using a watch window Try different test values to see which ones fail • Note: Max 2 marks