3.1 Computers & Components
AS Level · 3 questions found
What this topic covers
Section titled “What this topic covers”- Input, output, primary memory and secondary (removable) storage
- Embedded systems: benefits and drawbacks
- Hardware devices: laser/3D printer, microphone, speakers, HDD, SSD, optical, touchscreen, VR headset
- Buffers; RAM vs ROM; SRAM vs DRAM differences and use cases
- PROM, EPROM, EEPROM differences
- Monitoring vs control systems; sensors (temperature, pressure, IR, sound), actuators, feedback
Past paper questions
Section titled “Past paper questions” Q2

2
A video doorbell is attached to the front door of a house. The doorbell uses a motion sensor to
detect when a visitor walks in front of the door. When the motion sensor is activated:
•
The digital camera in the doorbell starts recording a video.
•
A message is transmitted to a smartphone so that the person who lives in the house can
watch the video.
The doorbell also has a button that can be pressed. When the button is pressed, a message is
transmitted to a smartphone to play the doorbell sound.
The videos are stored on the doorbell’s internal secondary storage device and overwritten when
the secondary storage device is full.
(a) The video doorbell can be considered an example of an embedded system.
Identify two characteristics of the doorbell that suggest it is an embedded system.
1 ................................................................................................................................................
2 ................................................................................................................................................
[2]
(b) State whether the video doorbell is a monitoring system or a control system.
Justify your choice.
Monitoring or control system ....................................................................................................
Justification ...............................................................................................................................
[2]
(c) The video doorbell has both primary memory and secondary storage.
(i) Identify two items of data that the video doorbell will store in primary memory.
1 ........................................................................................................................................
2 ........................................................................................................................................
[2]
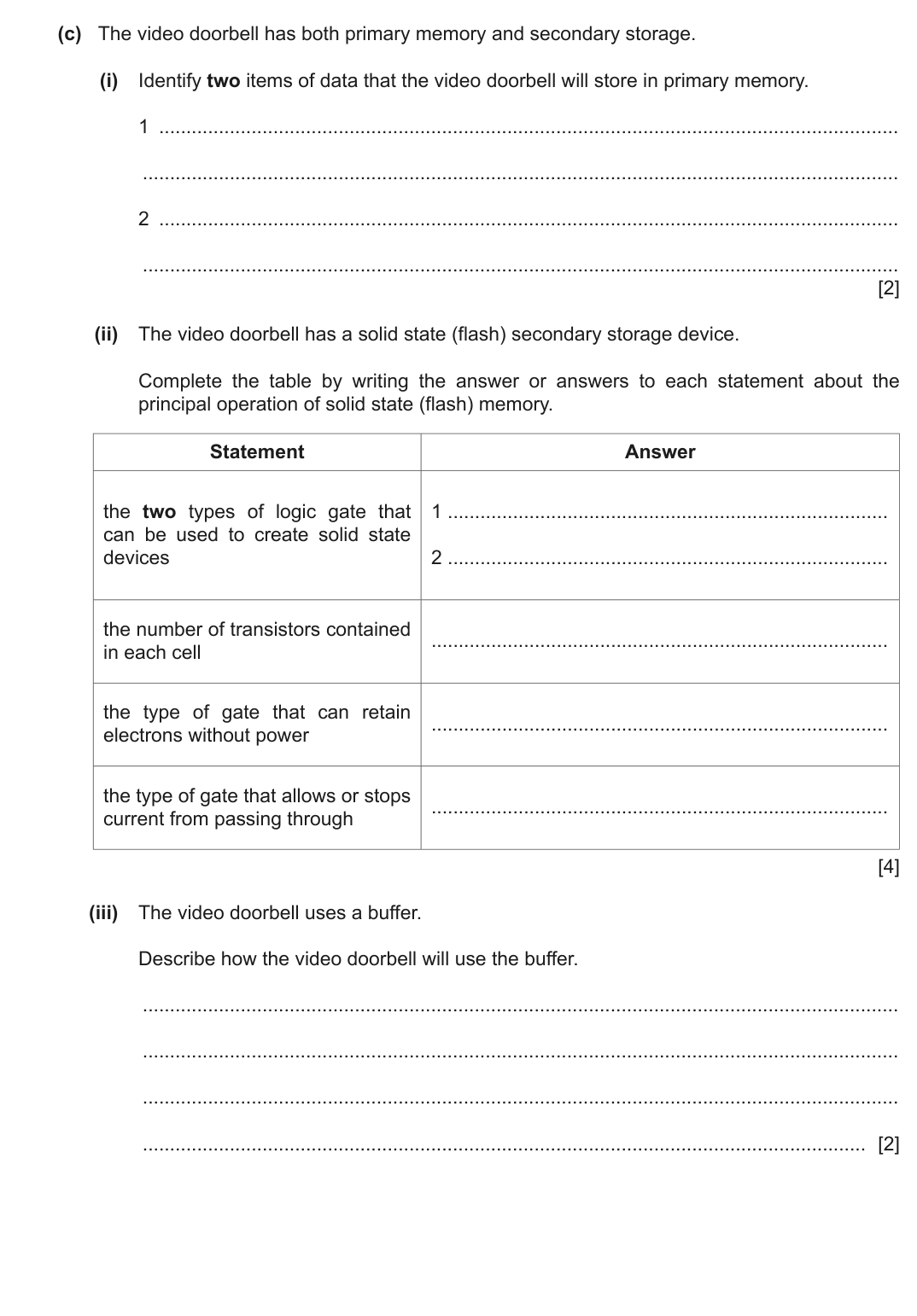
(ii) The video doorbell has a solid state (flash) secondary storage device.
Complete the table by writing the answer or answers to each statement about the
principal operation of solid state (flash) memory.
Statement
Answer
the two types of logic gate that
can be used to create solid state
devices
1 .................................................................................
2 .................................................................................
the number of transistors contained
in each cell
the type of gate that can retain
electrons without power
the type of gate that allows or stops
current from passing through
[4]
(iii) The video doorbell uses a buffer.
Describe how the video doorbell will use the buffer.
..................................................................................................................................... [2]
(d) The digital camera has a microphone which is used to record the sound for the video.
The user changes the sampling rate that the microphone uses from 44.1 kHz to 88.2 kHz.
Describe how this change in sampling rate will affect the performance of the video doorbell.
............................................................................................................................................. [3]
(e) The video doorbell allows both real-time and on-demand bit streaming.
(i) State what is meant by bit streaming.
..................................................................................................................................... [1]
(ii) Give two differences between real-time and on-demand bit streaming.
1 ........................................................................................................................................
2 ........................................................................................................................................
[2]
Show mark scheme
2(a) [2 marks]
1 mark
each
to max 2
:
The doorbell only performs the specific tasks of motion detection/video
recording/doorbell ringing
The motion sensor and digital camera are built into the doorbell
The CPU/memory/storage/software are all dedicated to this task only
Only a dedicated microprocessor is required due to the limited processing
requirements
each
to max 2
:
The doorbell only performs the specific tasks of motion detection/video
recording/doorbell ringing
The motion sensor and digital camera are built into the doorbell
The CPU/memory/storage/software are all dedicated to this task only
Only a dedicated microprocessor is required due to the limited processing
requirements
2(b) [2 marks]
No mark for identification of monitoring or control
1 mark
each to
max 2
for justification:
Monitoring:
The turning on of the digital camera does not affect the input to the
sensor/button
The transmission of the data/video does not affect the input to the
sensor/button
The ringing of the doorbell does not affect the input to the button
Control:
Video doorbell does not only store the values from the motion sensor
The data is processed, generating a signal to start the digital camera
recording
Button pressed/motion detected causes a signal to be sent over a
network to the smartphone
1 mark
each to
max 2
for justification:
Monitoring:
The turning on of the digital camera does not affect the input to the
sensor/button
The transmission of the data/video does not affect the input to the
sensor/button
The ringing of the doorbell does not affect the input to the button
Control:
Video doorbell does not only store the values from the motion sensor
The data is processed, generating a signal to start the digital camera
recording
Button pressed/motion detected causes a signal to be sent over a
network to the smartphone
2(c)(i) [2 marks]
1 mark
each to
max 2
:
Current reading/data from motion sensor
Current/recent video
Instructions being executed
Start-up/BIOS/boot-up instructions
each to
max 2
:
Current reading/data from motion sensor
Current/recent video
Instructions being executed
Start-up/BIOS/boot-up instructions
2(c)(ii) [4 marks]
1 mark
for each row:
Statement
The
two
types of logic gate that can be used to create solid
NAND
state devices
NOR
The number of transistors contained in each cell
2
The type of gate that can retain electrons without power
floating
The type of gate that allows or stops current from passing
control
through
for each row:
Statement
The
two
types of logic gate that can be used to create solid
NAND
state devices
NOR
The number of transistors contained in each cell
2
The type of gate that can retain electrons without power
floating
The type of gate that allows or stops current from passing
control
through
2(c)(iii) [2 marks]
1 mark
each to
max 2
:
Captured video is transmitted to buffer
… video is transmitted from buffer to smartphone
Store recent data in a buffer for the user to rewind
… instead of storing everything in secondary storage
Store readings from motion sensor
… until the microprocessor can process them
Store video from digital camera
… before moving it to secondary storage
each to
max 2
:
Captured video is transmitted to buffer
… video is transmitted from buffer to smartphone
Store recent data in a buffer for the user to rewind
… instead of storing everything in secondary storage
Store readings from motion sensor
… until the microprocessor can process them
Store video from digital camera
… before moving it to secondary storage
2(d) [3 marks]
1 mark
each to
max 3
:
Data transmission to user’s smartphone will take longer
… because there is more data to transmit
The secondary storage device will fill faster
… fewer videos will be able to be stored long-term // videos are
overwritten more often
each to
max 3
:
Data transmission to user’s smartphone will take longer
… because there is more data to transmit
The secondary storage device will fill faster
… fewer videos will be able to be stored long-term // videos are
overwritten more often
2(e)(i) [1 mark]
1 mark
for:
Continuous ordered flow of bits over a communication path
for:
Continuous ordered flow of bits over a communication path
2(e)(ii) [2 marks]
1 mark
each to
max 2
:
Real-time is direct from source whereas on-demand is pre-
recorded/downloaded to view later
Real-time cannot be re-watched, on-demand can be paused, re-watched
etc.
Real-time plays continually, on-demand downloads sections/blocks and
cannot play until next section is downloaded
each to
max 2
:
Real-time is direct from source whereas on-demand is pre-
recorded/downloaded to view later
Real-time cannot be re-watched, on-demand can be paused, re-watched
etc.
Real-time plays continually, on-demand downloads sections/blocks and
cannot play until next section is downloaded
Q2

2
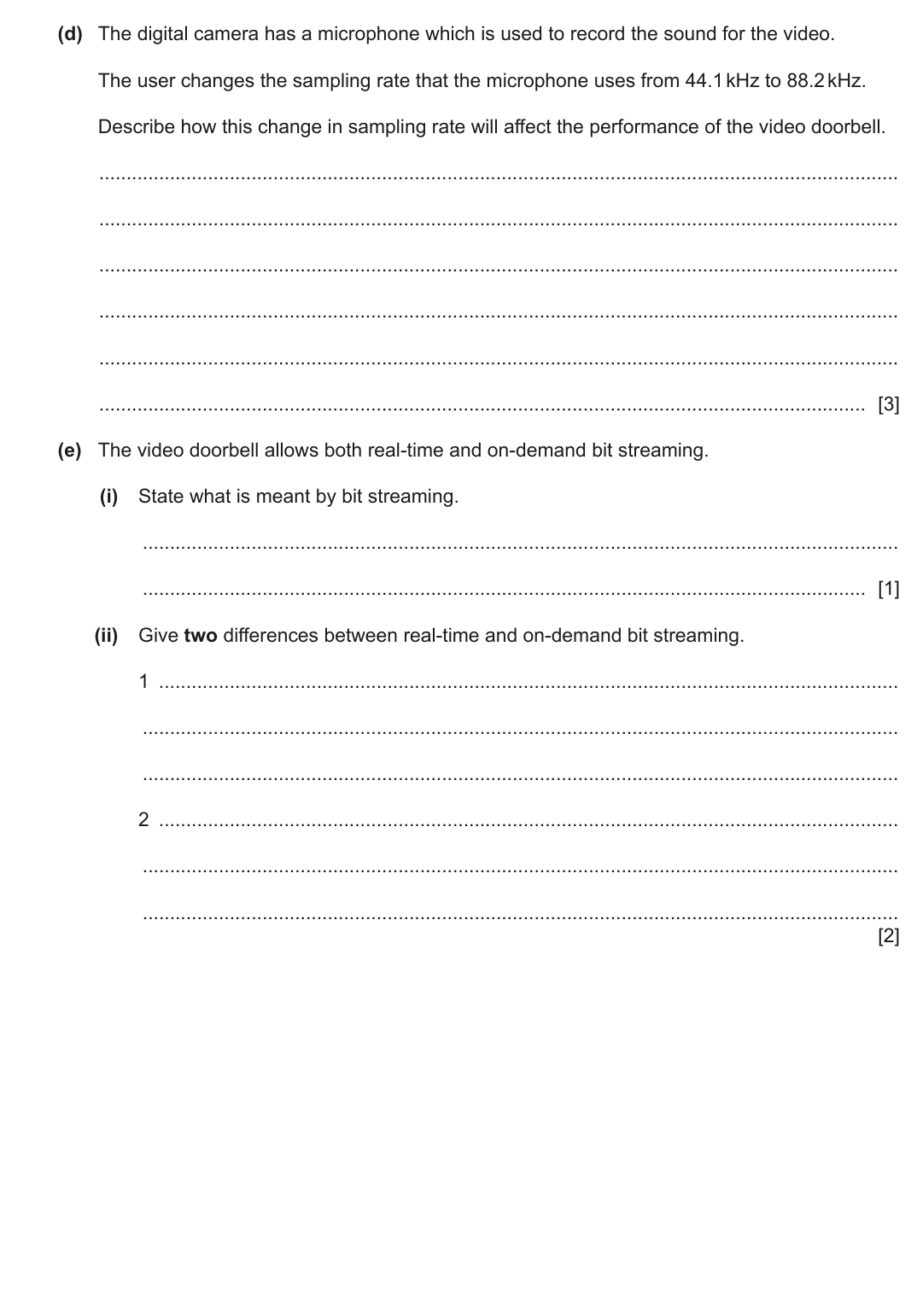
A computer game is being designed that users will be able to play using a virtual reality (VR)
headset.
(a) Complete the description of the principal operation of a VR headset.
A headset can have one or two .......................................................... that output the image to
the user. The headset has speakers that output surround sound to give a realistic experience.
The user’s head movements are detected using a sensor.
This sensor is a .......................................................... . The data is transmitted to a
microprocessor that analyses the data to identify the .......................................................... of
movement. Some headsets use .......................................................... that record the user’s
eye movements for analysis.
[4]
(b) The computer uses a buffer when transmitting data to the VR headset.
Explain how a buffer is used when data is transmitted between the computer and the VR
headset.
............................................................................................................................................. [3]
(c) The VR headset has Electrically Erasable Programmable Read Only Memory (EEPROM).
Explain the benefits of using EEPROM instead of other types of Read Only Memory (ROM) in
the VR headset.
............................................................................................................................................. [3]
(d) The computer can transmit a video made from bitmap images and vector graphic animations
to the VR headset.
(i) Describe how the data for a bitmapped image is encoded.
..................................................................................................................................... [3]
(ii) Describe the contents of a vector graphic drawing list.
..................................................................................................................................... [2]
(iii) The bitmap video is not compressed before transmission to the VR headset.
Give two reasons why the video does not need to be compressed.
1 ........................................................................................................................................
2 ........................................................................................................................................
[2]
Show mark scheme
2(a) [3 marks]
1 mark
for each correctly completed statement:
(
LCD) displays/screens/lenses
gyroscope/accelerometer
direction/speed
digital cameras
A headset can have one or two
(LCD) displays/screens/lenses
that output
the image to the user. The headset has speakers that output surround sound
to give a realistic experience.
The user's head movements are detected using a sensor.
This sensor is a
gyroscope/accelerometer
. The data is transmitted to a
microprocessor that analyses the data to identify the
direction/speed
of
movement. Some headsets use
digital cameras
that record the user's eye
movements for analysis.
for each correctly completed statement:
(
LCD) displays/screens/lenses
gyroscope/accelerometer
direction/speed
digital cameras
A headset can have one or two
(LCD) displays/screens/lenses
that output
the image to the user. The headset has speakers that output surround sound
to give a realistic experience.
The user's head movements are detected using a sensor.
This sensor is a
gyroscope/accelerometer
. The data is transmitted to a
microprocessor that analyses the data to identify the
direction/speed
of
movement. Some headsets use
digital cameras
that record the user's eye
movements for analysis.
2(b)
1 mark
each to
max 3
:
The buffer is used as a
temporary
store for data going to the headset
Data is
transferred
into the buffer by the computer
Data is
retrieved
from the buffer by the headset
When the buffer is empty/full an interrupt is sent to the computer
requesting more data/stopping further data being sent
When the headset has enough data/needs more data, an interrupt is sent
by the headset to the computer to stop sending data from buffer
each to
max 3
:
The buffer is used as a
temporary
store for data going to the headset
Data is
transferred
into the buffer by the computer
Data is
retrieved
from the buffer by the headset
When the buffer is empty/full an interrupt is sent to the computer
requesting more data/stopping further data being sent
When the headset has enough data/needs more data, an interrupt is sent
by the headset to the computer to stop sending data from buffer
2(c) [3 marks]
1 mark
each to
max 3
:
EEPROM allows
frequent/multiple
read/write/erase operations
… so the headset can take advantage of new features
… without fully erasing the contents of the firmware in the headset first //
can erase a particular byte or the whole EEPROM
… without removing the chip(s)/firmware from the headset
... the contents of the firmware in the headset can be changed by the user
without technical expertise
Cheaper to manufacture so headset will be cheaper to purchase
each to
max 3
:
EEPROM allows
frequent/multiple
read/write/erase operations
… so the headset can take advantage of new features
… without fully erasing the contents of the firmware in the headset first //
can erase a particular byte or the whole EEPROM
… without removing the chip(s)/firmware from the headset
... the contents of the firmware in the headset can be changed by the user
without technical expertise
Cheaper to manufacture so headset will be cheaper to purchase
2(d)(i) [3 marks]
1 mark
each:
Image is made of pixels and each pixel has one colour
Each colour has a
unique
binary code
Code for the colour
of each pixel is stored in
sequence
each:
Image is made of pixels and each pixel has one colour
Each colour has a
unique
binary code
Code for the colour
of each pixel is stored in
sequence
2(d)(ii) [2 marks]
1 mark
each to
max 2
:
List of objects in the drawing
A list that stores the command/description/equation required to draw each
object
Properties of each object e.g. the fill colour, line weight/colour
each to
max 2
:
List of objects in the drawing
A list that stores the command/description/equation required to draw each
object
Properties of each object e.g. the fill colour, line weight/colour
2(d)(iii) [3 marks]
1 mark
each to
max 2
:
Dedicated connection to the headset // not sharing bandwidth
Already fast connection that can transmit the data without slowing
Video may already be a small file size and does not need further
reduction
Video is not saved so storage is not an issue in the headset
each to
max 2
:
Dedicated connection to the headset // not sharing bandwidth
Already fast connection that can transmit the data without slowing
Video may already be a small file size and does not need further
reduction
Video is not saved so storage is not an issue in the headset
Q7
7
Robots are used to serve food and drink to customers at a restaurant.
(a) A robot navigates through the restaurant to the table it is serving.
Complete the table by identifying two sensors that can be included in the robot and the
purpose of each sensor in the navigation system.
Sensor
Purpose of sensor in navigation system
[2]
(b) The robot uses Artificial Intelligence (AI) to communicate with the customers. The customers
speak to the robot to order their food and drinks.
Explain how AI will be used in this part of the robot.
(c) The navigation system can be considered an example of a control system.
Describe how feedback is used in a control system.
............................................................................................................................................. [2]
(d) The robot includes a touchscreen for the customer to make their payment.
Describe the principal operation of a touchscreen.
............................................................................................................................................. [4]
,
,
(e) Program libraries were used when writing the robot’s software.
(i) State what is meant by a program library.
..................................................................................................................................... [1]
(ii) Some program libraries include Dynamic Link Library (DLL) files.
Describe the benefits of a programmer using a library with DLL files instead of using a
library that does not include DLL files.
..................................................................................................................................... [4]
,
,
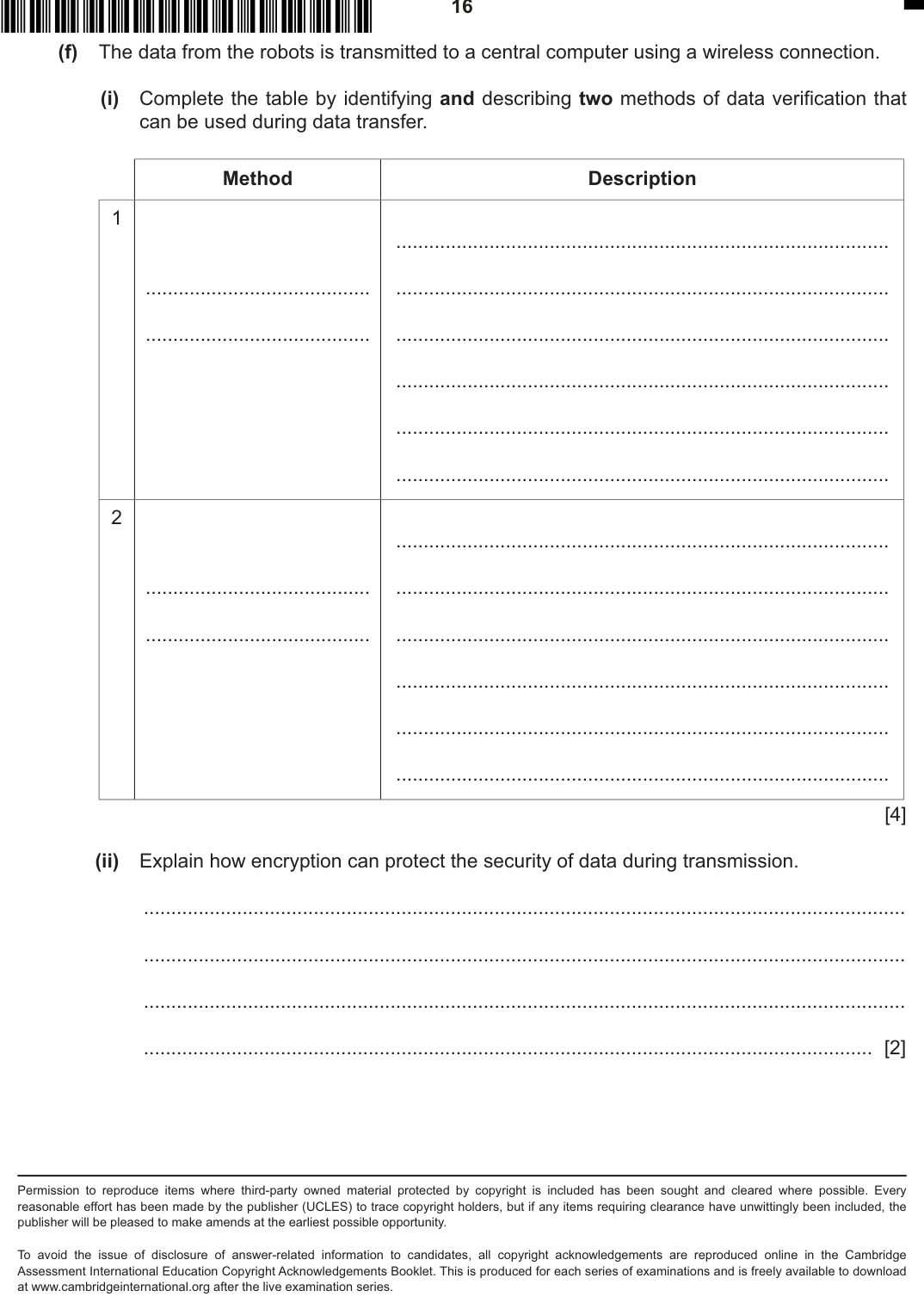
(f) The data from the robots is transmitted to a central computer using a wireless connection.
(i) Complete the table by identifying and describing two methods of data verification that
can be used during data transfer.
Method
Description
1
2
[4]
(ii) Explain how encryption can protect the security of data during transmission.
..................................................................................................................................... [2]
Permission to reproduce items where third-party owned material protected by copyright is included has been sought and cleared where possible. Every
reasonable effort has been made by the publisher (UCLES) to trace copyright holders, but if any items requiring clearance have unwittingly been included, the
publisher will be pleased to make amends at the earliest possible opportunity.
To avoid the issue of disclosure of answer-related information to candidates, all copyright acknowledgements are reproduced online in the Cambridge
Assessment International Education Copyright Acknowledgements Booklet. This is produced for each series of examinations and is freely available to download
at www.cambridgeinternational.org after the live examination series.
,
,
Show mark scheme
7(a) [2 marks]
1 mark
for sensor
and
matching purpose to
max 2
:
Sensor
Purpose of sensor in navigation system
Pressure
To detect if a table or other obstacle has been hit // to detect
when food is put on/taken off the tray so it can move on
Infra-red
To detect if there is an obstacle in the way // to indicate that it
has reached the desired table
Sound
To detect if someone is speaking so that it can use AI to
decipher the speech and whether the robot is required to stop
for sensor
and
matching purpose to
max 2
:
Sensor
Purpose of sensor in navigation system
Pressure
To detect if a table or other obstacle has been hit // to detect
when food is put on/taken off the tray so it can move on
Infra-red
To detect if there is an obstacle in the way // to indicate that it
has reached the desired table
Sound
To detect if someone is speaking so that it can use AI to
decipher the speech and whether the robot is required to stop
7(b) [2 marks]
1 mark
each to
max 3
:
e.g.
Voice/speech recognition is used
... to identify if someone speaking
The sound is recorded and analysed
The audio recordings are compared to a database of words/sound waves
... to identify the word that has the highest probability of being said
Natural language recognition is used
Words are combined and compared to known sentences
… programmed action(s) for matching sentence(s) are performed
each to
max 3
:
e.g.
Voice/speech recognition is used
... to identify if someone speaking
The sound is recorded and analysed
The audio recordings are compared to a database of words/sound waves
... to identify the word that has the highest probability of being said
Natural language recognition is used
Words are combined and compared to known sentences
… programmed action(s) for matching sentence(s) are performed
7(c)
1 mark
each to
max 2
:
Feedback ensures that a system operates within set criteria / constraints
... by enabling system output to affect subsequent system input
... thus allowing conditions to be
automatically
adjusted
each to
max 2
:
Feedback ensures that a system operates within set criteria / constraints
... by enabling system output to affect subsequent system input
... thus allowing conditions to be
automatically
adjusted
7(d) [1 mark]
1 mark
each to
max 4
:
Resistive: The space between the conductive layers is removed/the
layers touch and a circuit is completed
Capacitive: The electrical charge changes where the user pressed
The point of contact is identified
... from the change in electrical field
The software/microprocessor
calculates
the coordinates
each to
max 4
:
Resistive: The space between the conductive layers is removed/the
layers touch and a circuit is completed
Capacitive: The electrical charge changes where the user pressed
The point of contact is identified
... from the change in electrical field
The software/microprocessor
calculates
the coordinates
7(e)(i)
1 mark
for:
Pre-written code/functions/routines that can be
imported/called
in another
program
for:
Pre-written code/functions/routines that can be
imported/called
in another
program
7(e)(ii) [4 marks]
1 mark
each to
max 4
:
Maintenance not needed to be done by the programmer
... because the DLL is separate from program
The calling program does not need recompilation by the programmer when
a DLL file changes
... because the DLL file can be updated independently of the calling
program
… updates will apply to all programs that use the DLL file
each to
max 4
:
Maintenance not needed to be done by the programmer
... because the DLL is separate from program
The calling program does not need recompilation by the programmer when
a DLL file changes
... because the DLL file can be updated independently of the calling
program
… updates will apply to all programs that use the DLL file
7(f)(i) [4 marks]
1 mark
for each correct method and
1 mark
for corresponding description to
max 4
:
Method
Description
Parity byte
An additional bit is added to make the number of 1s in the
byte odd or even to match the parity. If a byte with an odd
number of 1 bits is received when even parity is used, there is
an error.
Parity block Parity is calculated horizontally and vertically. A parity byte is
created from the bits produced by the vertical parity check.
This is sent with the data. The parity is re-checked when
received and the position of an incorrect bit can be
determined.
Checksum
A calculation is made from the data and the result transmitted
with the data. The receiver repeats the calculation and
compares the result with the value received. If the two are
different, there is an error.
for each correct method and
1 mark
for corresponding description to
max 4
:
Method
Description
Parity byte
An additional bit is added to make the number of 1s in the
byte odd or even to match the parity. If a byte with an odd
number of 1 bits is received when even parity is used, there is
an error.
Parity block Parity is calculated horizontally and vertically. A parity byte is
created from the bits produced by the vertical parity check.
This is sent with the data. The parity is re-checked when
received and the position of an incorrect bit can be
determined.
Checksum
A calculation is made from the data and the result transmitted
with the data. The receiver repeats the calculation and
compares the result with the value received. If the two are
different, there is an error.
7(f)(ii) [2 marks]
1 mark
each to
max 2
:
Encodes/scrambles data
... so if it is intercepted it cannot be
understood
Algorithm
/key
is required to decode the data
each to
max 2
:
Encodes/scrambles data
... so if it is intercepted it cannot be
understood
Algorithm
/key
is required to decode the data