6.2 Data Integrity
AS Level · 2 questions found
What this topic covers
Section titled “What this topic covers”- How validation and verification protect data integrity
- Validation methods: range, format, length, presence, existence, limit check, check digit
- Verification during data entry: visual check, double entry
- Verification during data transfer: parity check (byte and block), checksum
Past paper questions
Section titled “Past paper questions” Q5

5
A bank allows customers to access their accounts using an application that they can download
onto a device such as a smartphone.
(a) The system that allows customers to access their accounts using the application is a
client-server model.
Describe the roles of the different devices in this model.
............................................................................................................................................. [4]
(b) The bank wants to protect the integrity of its data while transferring the data to other banks.
Parity check is one example of data verification.
Complete the description of parity check when Computer A is transmitting data to Computer B.
Computer A and Computer B agree on whether to use ......................................................
parity. Computer A divides the data into groups of ...................................................... . The
number of 1s in each group is counted. If the agreed parity is ................................................
and the group has an even number of 1s, a parity bit of 1 is appended, otherwise a parity bit
of 0 is appended.
In a parity ...................................................... check the bytes are grouped together, for
example in a grid. The number of 1s in each column (bit position) is counted. A bit is assigned
to each column to make the column match the parity. These parity bits are transmitted with
the data as a parity ...................................................... .
[5]
(c) The bank also needs to keep its customers’ data private and secure.
(i) The bank’s network has a firewall.
Explain how a firewall can help protect the customers’ data.
..................................................................................................................................... [3]
(ii) Customers need to use biometric authentication to access their accounts.
One biometric authentication method is facial recognition.
Facial recognition uses Artificial Intelligence (AI).
Describe how AI is used in facial recognition.
..................................................................................................................................... [4]
Show mark scheme
5(a) [4 marks]
1 mark
each:
Identification of server in the bank scenario
Description e.g. Receives requests, processes the requests
Identification of client in bank scenario
Description e.g. Sends request to the server, waits and outputs the
response
each:
Identification of server in the bank scenario
Description e.g. Receives requests, processes the requests
Identification of client in bank scenario
Description e.g. Sends request to the server, waits and outputs the
response
5(b) [5 marks]
1 mark
for each correctly completed term:
odd or even
7-bits
odd
block
byte
Computer A and Computer B agree on whether to use
odd or even
parity.
Computer A divides the data into groups of
7-bits
. The number of 1s in each
group is counted. If the agreed parity is
odd
and the group has an even
number of 1s a parity bit of 1 is appended, otherwise a parity bit of 0 is
appended.
In a parity
block
check the bytes are grouped together, for example in a grid.
The number of 1s in each column (bit position) is counted. A bit is assigned to
each column to make the column match the parity. These parity bits are
transmitted with the data as a parity
byte
.
for each correctly completed term:
odd or even
7-bits
odd
block
byte
Computer A and Computer B agree on whether to use
odd or even
parity.
Computer A divides the data into groups of
7-bits
. The number of 1s in each
group is counted. If the agreed parity is
odd
and the group has an even
number of 1s a parity bit of 1 is appended, otherwise a parity bit of 0 is
appended.
In a parity
block
check the bytes are grouped together, for example in a grid.
The number of 1s in each column (bit position) is counted. A bit is assigned to
each column to make the column match the parity. These parity bits are
transmitted with the data as a parity
byte
.
5(c)(i) [3 marks]
1 mark
each to
max 3
:
Compares all incoming and outgoing transmissions
... against set criteria/whitelist/blacklist
Blocks all transmissions that do not meet rules
Blocks data entering from specific ports
Blocks unauthorised/unknown internal software transmitting data
each to
max 3
:
Compares all incoming and outgoing transmissions
... against set criteria/whitelist/blacklist
Blocks all transmissions that do not meet rules
Blocks data entering from specific ports
Blocks unauthorised/unknown internal software transmitting data
5(c)(ii) [4 marks]
1 mark
each to
max 4
:
e.g.
Captures an image of the face
Uses image recognition
Trained to identify the features of a face in an image
… using a large number of images
Analyse images for facial features
Uses the probability of a match
each to
max 4
:
e.g.
Captures an image of the face
Uses image recognition
Trained to identify the features of a face in an image
… using a large number of images
Analyse images for facial features
Uses the probability of a match
Q3

3
An assessment board scans exam papers and stores the digitised papers on a server. Exam
markers download the digitised papers to mark. The exam markers then upload the mark for each
paper.
(a) The assessment board needs to make sure the data stored on the server is secure.
(i) Authentication methods can help to protect the server against hackers.
Identify one other security measure that helps to protect the server from hackers.
Describe how the security measure works.
Security measure ..............................................................................................................
Description ........................................................................................................................
[3]
(ii) Identify one security measure that helps to protect the data when it is being transmitted
to its destination. Describe how the security measure works.
Security measure ..............................................................................................................
Description ........................................................................................................................
[3]
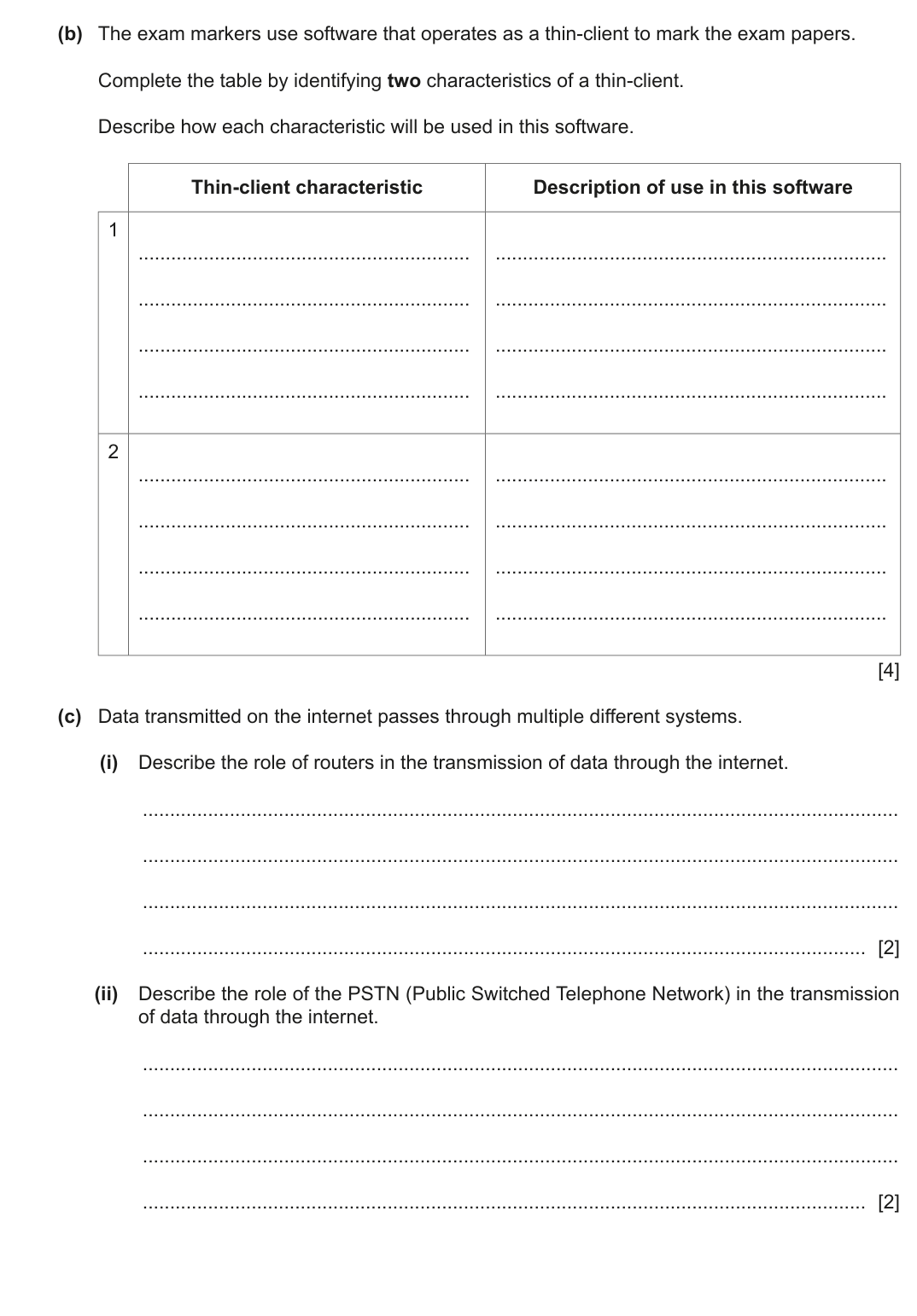
(b) The exam markers use software that operates as a thin-client to mark the exam papers.
Complete the table by identifying two characteristics of a thin-client.
Describe how each characteristic will be used in this software.
Thin-client characteristic
Description of use in this software
1
2
[4]
(c) Data transmitted on the internet passes through multiple different systems.
(i) Describe the role of routers in the transmission of data through the internet.
..................................................................................................................................... [2]
(ii) Describe the role of the PSTN (Public Switched Telephone Network) in the transmission
of data through the internet.
..................................................................................................................................... [2]
Show mark scheme
3(a)(i)
1 mark
for security measure
1 mark
each to
max 2
for how the chosen measure works:
Firewall
Checks
incoming
connections
... against criteria
Blocks data from entering specific ports
Blocks data that does not meet whitelist that meets blacklist
Proxy server
Prevents devices accessing the web server directly
Intercepts any requests
Forwards the request using its own IP address
Screens returning data before sending it to the user
for security measure
1 mark
each to
max 2
for how the chosen measure works:
Firewall
Checks
incoming
connections
... against criteria
Blocks data from entering specific ports
Blocks data that does not meet whitelist that meets blacklist
Proxy server
Prevents devices accessing the web server directly
Intercepts any requests
Forwards the request using its own IP address
Screens returning data before sending it to the user
3(a)(ii) [3 marks]
1 mark
for security measure
1 mark
each to
max 2
for description of the chosen measure:
Encryption
Encodes/scrambles data
... so if it is intercepted it cannot be
understood
Algorithm/key is required to decode
the data
for security measure
1 mark
each to
max 2
for description of the chosen measure:
Encryption
Encodes/scrambles data
... so if it is intercepted it cannot be
understood
Algorithm/key is required to decode
the data
3(b) [4 marks]
1 mark
for characteristic
1 mark
for description of application to examination software:
Thin-client characteristic
Description of use in this software
Data is not stored on the
Exam papers are stored on the server and
client computer
not on the examiner’s computer // exam
papers are not permanently stored on the
examiners’ computers
Client computer is reliant on
Examiners cannot mark if their device
access to server
cannot access the server / the server ‘goes
down’
The marking software will not operate
Client computer heavily
without network/internet access
reliant on network/internet
connection
Client computer requires few
Examiners can use devices with low
local resources/memory
resources and the marking software will still
function
Client computer performs
The marking software transmits requests,
minimal functions/processes
the server responds and sends the
response to the user
for characteristic
1 mark
for description of application to examination software:
Thin-client characteristic
Description of use in this software
Data is not stored on the
Exam papers are stored on the server and
client computer
not on the examiner’s computer // exam
papers are not permanently stored on the
examiners’ computers
Client computer is reliant on
Examiners cannot mark if their device
access to server
cannot access the server / the server ‘goes
down’
The marking software will not operate
Client computer heavily
without network/internet access
reliant on network/internet
connection
Client computer requires few
Examiners can use devices with low
local resources/memory
resources and the marking software will still
function
Client computer performs
The marking software transmits requests,
minimal functions/processes
the server responds and sends the
response to the user
3(c)(i) [2 marks]
1 mark
each to
max 2
:
Receives
packets
from internet
Analyses the destination IP address of each packet
Forwards the
packet
towards its destination
... using the routing table
Maintains/updates the routing table
Finds the most efficient route to the destination
each to
max 2
:
Receives
packets
from internet
Analyses the destination IP address of each packet
Forwards the
packet
towards its destination
... using the routing table
Maintains/updates the routing table
Finds the most efficient route to the destination
3(c)(ii) [1 mark]
1 mark
each to
max 2
:
The PSTN consists of many different types of communication lines
… therefore the digital data may need to be converted into a different
form/analogue signal
Data is transmitted in both directions at the same time // duplex data
transmission
Using a PSTN the communication passes through different switching
centres/ISPs
each to
max 2
:
The PSTN consists of many different types of communication lines
… therefore the digital data may need to be converted into a different
form/analogue signal
Data is transmitted in both directions at the same time // duplex data
transmission
Using a PSTN the communication passes through different switching
centres/ISPs